Real-World Attacks. Expert Insight. Actionable Outcomes.
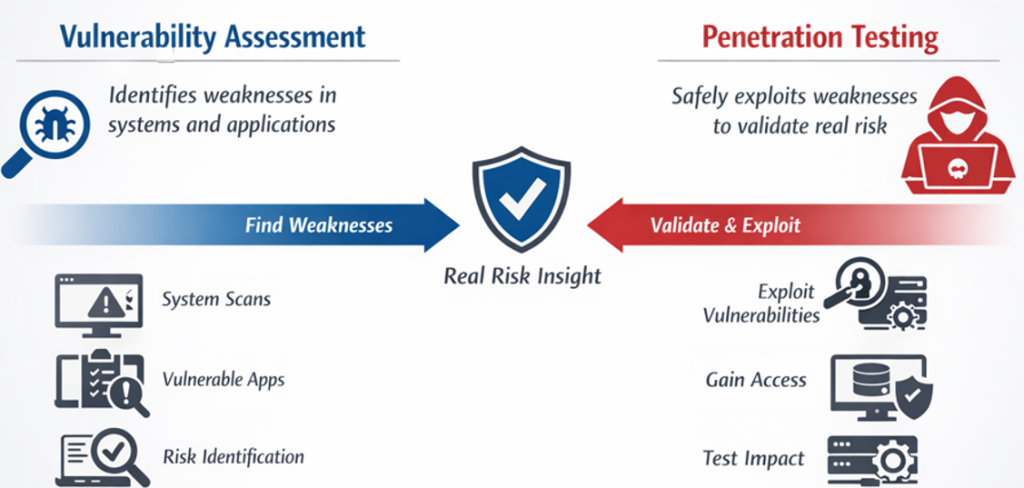
Penetration Testing Assessment is a structured security evaluation where certified cybersecurity professionals simulate real-world attack scenarios to identify exploitable weaknesses across your IT environment.
Unlike automated vulnerability scans, penetration testing focuses on how vulnerabilities can actually be chained and abused, providing context-aware findings that reflect real attacker behavior.
SecureNow’s approach combines manual testing expertise with tool-assisted discovery, delivering validated findings, clear risk prioritization, and practical remediation guidance tailored to your environment.
Why You Need A Penetration Testing?

- Identify Security Gaps Before They Are Exploited
Proactively uncover exploitable weaknesses across networks, applications, APIs, and cloud environments before attackers can take advantage of them. Validate the Effectiveness of Existing Security Controls
Assess whether current security measures are correctly configured and effective against real-world attack scenarios.Reduce the Risk of Data Breach and Service Disruption
Identify high-impact vulnerabilities that could lead to operational downtime, data loss, or business interruption.
What Does a Penetration Testing Assessment Cover?
Network & server VAPT
Identify exposed services, misconfigurations, and lateral movement risks across internal and external networks.
Web & Application VAPT
Detect common and advanced vulnerabilities such as injection flaws, authentication bypass, and access control weaknesses.
Cloud & Server Environment Assessment
Evaluate cloud workloads and servers for configuration gaps, privilege exposure, and attack paths unique to hybrid environments.
API Security Testing
Evaluate REST and application APIs for improper authorization, data exposure, and logic weaknesses commonly targeted in modern attacks.
Test Your Defenses.
Uncover Weaknesses.
Strengthen Security.
Why SecureNow?
Human-Led Testing
Certified security professionals go beyond automated tools to uncover logic flaws, attack chains, and real exploitation paths.
Rapid Engagement Kickoff
Standardized scoping and onboarding enable faster assessment start times compared to traditional, consultant-heavy models.
Verified Findings Only
Every reported issue is validated by security experts, reducing false positives and remediation fatigue.
Compliance-Aligned Reporting
Clear, structured reports suitable for internal risk reviews and common audit requirements
How it works?

Scoping & Authorization
Define objectives, scope boundaries, and testing rules aligned with business and operational requirements.

Discovery & Reconnaissance
Identify exposed services, applications, and attack surfaces within the approved scope.

Vulnerability Analysis & Penetration Testing
Assess weaknesses and simulate controlled attack scenarios to determine real-world exploitability.

Results Review & Risk Validation
Validate findings, assess business impact, and eliminate false positives.

Reporting & Recommendations
Deliver a structured report with prioritized risks and practical remediation guidance.
Solution Certified Partner's
Trusted by the Technology You Use






















FAQ
Automated scanners identify potential issues. Penetration testing verifies whether those issues can actually be exploited and how much risk they pose in real-world attack scenarios.
Yes. Testing is conducted by experienced cybersecurity professionals holding industry-recognized certifications and practical offensive security experience.
Yes. Internal networks, private cloud environments, and restricted systems can be assessed through secure access methods agreed during scoping.
Testing activities are carefully planned and executed to minimize operational impact. Scope, timing, and testing intensity are agreed in advance to avoid disruption to critical systems and business processes.
You will receive a clear, professional report outlining identified vulnerabilities, validated risk levels, exploitation evidence (where applicable), and actionable remediation recommendations suitable for both technical teams and management.
Identify Weaknesses Before They Become Incidents
📩 Contact us today to learn how we can secure your business data.
