Your Security Perimeter in the Cloud
A Secure Web Gateway (SWG) acts as a security checkpoint between users and the internet. Unlike traditional firewalls that focus on ports and IP addresses, an SWG inspects web content itself — including encrypted traffic — to detect threats, enforce acceptable use policies, and protect sensitive data.
By inspecting web activity at the application and content level, SWG ensures consistent security controls for both on-site and remote users, regardless of location or device.
How a SWG Wokrs?
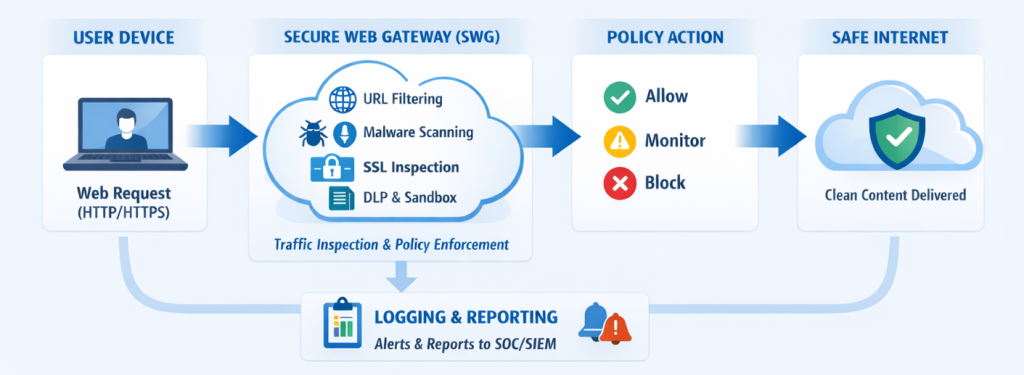
URL Filtering & Category Control
Block access to malicious, inappropriate, or high-risk website categories based on organizational policy.
Malware Scanning & Sandboxing
Detect and analyze suspicious files and web content before they reach end users.
SSL/TLS Inspection
Inspect encrypted web traffic to uncover hidden threats without compromising performance.
Phishing & Malicious Site Blocking
Prevent access to known phishing sites & malicious infrastructure using continuously updated threat intelligence.
Data Loss Prevention (DLP)
Identify & block unauthorized transmission of sensitive information.
Why It Matters?
Business Benefits
Enterprise-Grade.
Scalable.
Cost-Effective.
Why Us
Security-First Architecture Design
We design SWG policies around real threat scenarios — phishing campaigns, malicious downloads, and data exfiltration paths — not generic category blocking. This ensures protection without disrupting daily business operations.
Practical Visibility & Control
Our approach emphasizes actionable visibility. Security teams gain clear insight into web usage, blocked threats, and policy effectiveness, enabling informed decision-making instead of alert fatigue.
Built for Hybrid & Remote Workforces
We design SWG deployments to protect users wherever they work — office, home, or on the move — with consistent policy enforcement and centralized control across locations.
Operational Support & Expert Guidance
From policy definition to ongoing optimization, our team supports your security operations with expert guidance, helping you adapt to new threats, compliance needs, and business changes over time.
Use Cases
Hybrid Workforce Protection
Secure internet access for employees working in offices, branches, or remote locations.
Shadow IT Visibility
Identify unauthorized cloud services and web applications being used within the organization.
Productivity & Bandwidth Optimization
Limit access to non-business-related or high-bandwidth sites to prioritize critical applications.
Solution Certified Partner's
Trusted by the Technology You Use






















FAQ
No. The solution is designed to inspect encrypted traffic efficiently, with minimal impact on user experience.
Yes. Policies can be customized based on roles, departments, locations, or user identity.
Sensitive categories can be excluded from inspection using policy-based bypass rules to maintain user privacy and compliance.
Yes. Security policies can be enforced through cloud-based gateways or endpoint-based enforcement, ensuring protection even when users are off-network.
Yes. The Secure Web Gateway is scalable and can support small teams as well as large, distributed enterprises.
Turn Your Employees into Your First Line of Defense
📩 Contact SecureNow today to learn more about our Security Awareness Training programs.