Know Ur Risks Before They Become Realities.
- analysis
- Why Needed?
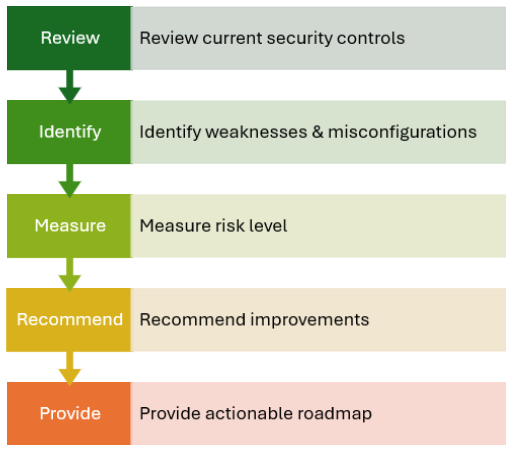
Security Assessment Services is a structured and holistic review of your organization’s cybersecurity posture across technology, processes, and governance.
Unlike a simple automated vulnerability scan, this assessment integrates technical validation, policy analysis, configuration reviews, and stakeholder discussions. Your current environment is evaluated against recognized frameworks to determine maturity level, control effectiveness, and exposure to operational or compliance risk.
Many organization face common & recurring challenges:
Limited visibility into actual security gaps
- A reactive approach to incidents rather than proactive risk management
- Uncertainty around compliance obligations
- Overlapping tools with unclear effectiveness
- Limited security manpower and stretched IT teams

What We Do?
Without an independent and structured evaluation, it becomes difficult to prioritize investment, justify budget, or demonstrate governance to management and regulators. Security Assessment Services bridges that gap by providing measurable insight into your current state and a realistic path forward.
deliverables
- Executive Summary for management review
- Detailed Findings Report with technical evidence
- Risk Matrix
- Gap Register aligned to standards and best practices
- Prioritized Improvement Roadmap
- Presentation Session to senior stakeholders
Identify Risks.
Strengthen Defense.
Stay Secure.
Why Us?
Designed for Real-World Operations
Holistic Vulnerability Discovery
We assess infrastructure, cloud configurations, identity controls, governance frameworks, and user behavior to uncover real exposure points.
Business-Aligned Risk Scoring
We translate technical findings into business language, clarifying how vulnerabilities impact operations, compliance, and financial stability.
Practical Remediation Planning
We do not stop at identifying issues. We provide prioritized and achievable recommendations aligned with your resources.
Vendor-Neutral Perspective
Our goal is objective assessment, not hardware sales. Recommendations are based on risk reduction and operational practicality.
Business Benefits
Security Assessment Services enables organizations to:
Reduce breach likelihood through proactive gap identification
Strengthen executive visibility into cyber risk
Meet compliance and regulatory expectations
Use Cases
Pre-Audit Preparation
Post-Incident Review
Mergers & Acquisitions Due Diligence
Annual Security Strategy Planning
Solution Certified Partner's
Trusted by the Technology You Use






















FAQ
Depending on organizational size and scope, assessments typically range from two weeks to two months.
No. Technical reviews are conducted in a controlled manner, and policy evaluations are performed through documentation reviews and interviews to minimize impact.
No. A penetration test focuses on actively exploiting vulnerabilities. A security assessment is broader — evaluating infrastructure, governance, compliance alignment, and overall security maturity.
Yes. Findings and gap analysis can be aligned with standards such as ISO 27001, PDPA, and other regulatory frameworks.
